
|
Today we announce the general availability of AWS WAF integunction with AWS amplify hosting.
Web applications are constantly working to protect their applications from various threats. Previously, if you want to implement a robust body posture for your hosted amplify applications, you need to create architectures using Amazon Cloudfront with AWS WAF Protection, which required further configuration steps, expertise and management.
With the general availability of AWS WAF in Amplify Hosting, you can now directly connect the Firewall web applications to AWS Amplify via one click into the Amplify console or using the IAC (IAC) console. This integration provides you with access to a wide range of AWS WAF abilities, including managed rules that provide protection against common web exploitation and vulnerabilities such as SQL injection and scripting between location (XS). You can also create your own rules based on your specific applications needs.
This new ability will help you implement security strategies for your web applications. You can use the AWS WAF speed rules to protect against distributed attacks on the service rejection (DDOS) by limiting the speed requirements from IP addresses. In addition, you can implement geo-blocking into a restric access to your applications from a particular country, which is particularly valuable if your service is designed for specific geographical regions.
We’ll see that it works
The AWS WAF protection settings for your Amplify application is simple. From the Amplify console, go to the application settings Firewall Tab and select predefined rules you want to use for your configuration. 
Amplify Hosing simplifies the configuration of the firewall gate rules. You can activate four categories of protection.
- Amplify-Recomment Firewall Protection – Protect from the most common vulnerability found in web applications, block IP addresses from potential threats based on the intelligence of Amazon Intelligence Threat Intelligence, and protect against harmful actors discovering the vulnerability of applications.
- Limited access to amplifyApp.com – Restric access to the domain of amplifyApp.com amplify amplify amplify. This is useful if you add your own domain to prevent robots and search engines from browsing the domain.
- Allow IP address protection – Limit the web operation by enabling or blocking the requirements to a specific IP address range.
- Allow Earth Protection – Omassing based on specific countries.
Protection allowed via the Amplify console will create a basic AC access list (ACL) in your AWS account. For fine -grained rules, you can use the AWS WAF console creators.
After a few minutes, the rules are associated with your application and AWS WAF blocks suspicious requirements.
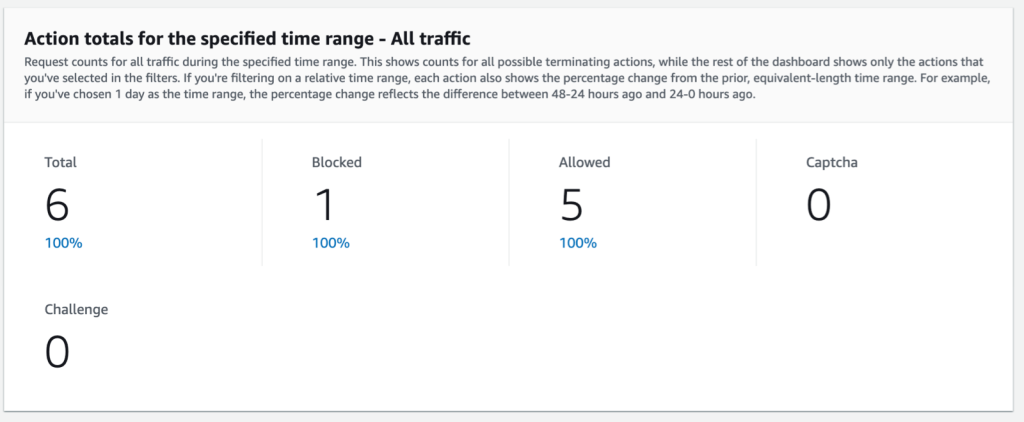
If you want to see AWS WAF in action, you can simulate the attack and monitor it using the AWS WAF application. For example, you can require an empty user of the agency. It starts the AWS WAF blocking rule.
Send a valid request to my application first.
curl -v -H "User-Agent: MyUserAgent" https://main.d3sk5bt8rx6f9y.amplifyapp.com/
* Host main.d3sk5bt8rx6f9y.amplifyapp.com:443 was resolved.
...(redacted for brevity)...
> GET / HTTP/2
> Host: main.d3sk5bt8rx6f9y.amplifyapp.com
> Accept: */*
> User-Agent: MyUserAgent
>
* Request completely sent off
< HTTP/2 200
< content-type: text/html
< content-length: 0
< date: Mon, 10 Mar 2025 14:45:26 GMT
We can observe that the server has returned HTTP 200 (OK) message.
Then send the request without the value associated with the HTTP header of the agency.
curl -v -H "User-Agent: " https://main.d3sk5bt8rx6f9y.amplifyapp.com/
* Host main.d3sk5bt8rx6f9y.amplifyapp.com:443 was resolved.
... (redacted for brevity) ...
> GET / HTTP/2
> Host: main.d3sk5bt8rx6f9y.amplifyapp.com
> Accept: */*
>
* Request completely sent off
< HTTP/2 403
< server: CloudFront
... (redacted for brevity) ...
<TITLE>ERROR: The request could not be satisfied</TITLE>
</HEAD><BODY>
<H1>403 ERROR</H1>
<H2>The request could not be satisfied.</H2>We can observe that the server has returned HTTP 403 (forbidden).
AWS WAF provides visibility in the request formulas and helps you fine -tune your security settings over time. You proceed to protocols via amplify hosting or AWS WAF and analyze traffic trends and specify security rules as needed.
Availability and Price
Firewall support is available in all AWS regions in which AMPLIFY hosting works. This integration falls into the global AWS WAF source, similar to Amazon Cloudfront. Web ACL can be connected to multiple AMPLIFY hosting applications, but there must be a stay in the same area.
Prices for this integration are governed by the standard AWS WAF price, you pay for AWS WAF sources that you use based on the number of web ACLs, rules and requirements. In addition, AWS Amplify Hosting adds $ 15/month when you connect to your Firewall Web app. This is praised by an hour.
This new capacity brings the security function of the Enterprise class of all amplify hosting customers, from individual developers to large businesses. Now you can build, host and protect your web applications within the same service and reduce the complexity of your architecture and make security management more efficient.
If you want to learn more, visit the AWS WAF integration documentation for amplify or try it directly in the Amplify console.
– seb
How’s the Blog of news? Take this 1 minute survey!
(This survey is hosted by an external company. AWS processes your information as described in the AWS Privacy Notice. AWS will own data collected via this survey and will not share information with dew survey.)

